Step-By-Step Process Involved in Ethical Hacking
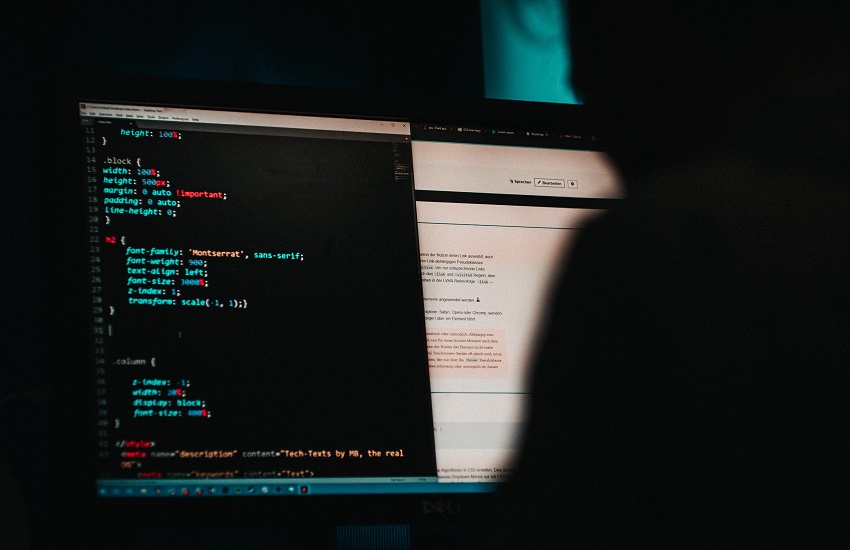
Ethical hacking has grown to become a key profession in the modern workplace. Digital systems have become common in workplaces across the board. Nothing can happen in a modern workplace without the use of digital systems.
The shift to digital from analog is necessary. The convenience of computers and the advantages of something as revolutionary as the internet are together factors which cannot be ignored.
This is despite considering the obvious threat of cyber-attacks. While movies and pop-culture may have exaggerated the role of hackers in the digital world. They are still a threat to companies which depend on digital systems to run their business. Also Know: Apparatus to Use for Trial Automation
Ethical Hacking Process – Complete Steps
To defend itself from the threat of cyber-attacks, a company must hire ethical hacker to maintain the cyber-security of their digital systems.
An Ethical Hacker follows the Following Step in Bringing Cyber Security to a System
Reconnaissance
In this step, ethical hackers analyze the system from a distance. This means gathering information about a digital system without the system’s admins noticing. Once the necessary information is gathered, ethical hackers proceed to establishing the goals of the process, the techniques they will be using to hack the system, and the potential vulnerabilities. The entire point of the process is to make the digital system experience what it would in a real cyber-attack.
Scanning
In scanning, the system is tested to see how it reacts to an attempt by an external party trying to infiltrate it. Ethical hackers generally do this by testing the system against either static or functioning application code.
Access
After scanning, an ethical hacker is able to pinpoint the exact weak points where the system is failing. By attacking these vulnerabilities through methods like SQL injections, cross-site scripting, backdoor entry, or any other viable technique, an ethical hacker gains access to the system.
Keeping Control
Once access is gained, the next challenge is maintaining control and access over the system. While doing this, ethical hackers seek to know the type of information they can steal after entering the system. Generally, this is the information most companies want to know when they hire ethical hackers. By keeping control, ethical hackers get an idea about the type of information which could be under threat in case of an intrusion.
Analysis
The final step is compiling all three different actions taken during the ethical hacking process by the ethical hacker. This also includes making a report on the different vulnerabilities in the system, the different information under threat from a potential cyber-attack, and how the system can be made secure from cyber-attacks.
In Conclusion
Ethical hacking is not a one-horse technique. It is an entire process and requires professionals to be methodical in their approach. In this article, I have presented a step-by-step approach to a typical ethical hacking process